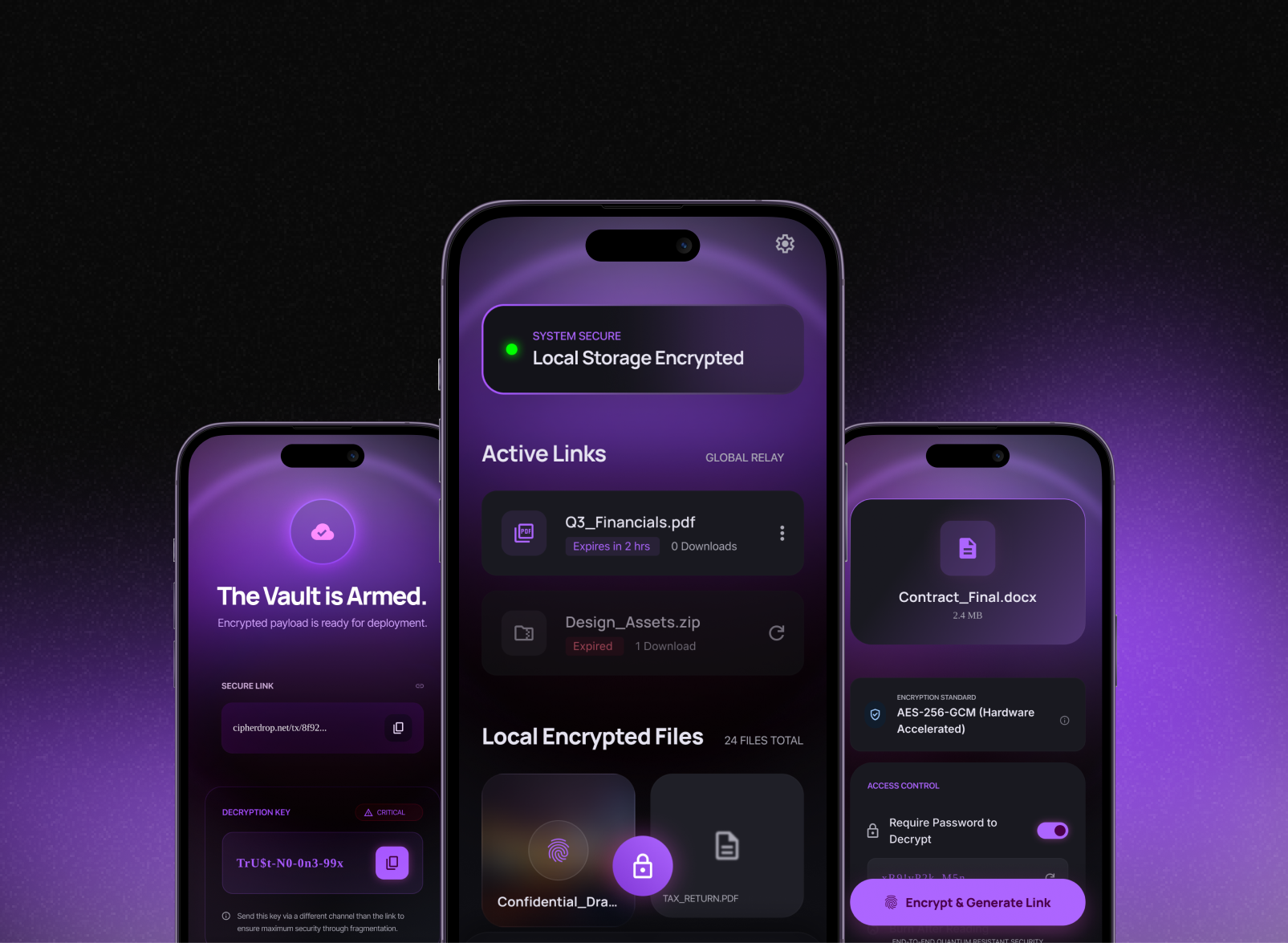
CipherDrop - Secure File Sharing
An app that performs military-grade local encryption on your device before a file ever touches the cloud or a network, generating secure, time-sensitive download links.


Mobile app security engineering that protects your users, your data, and your reputation — built in from the start.
Tools & Technologies
An app that performs military-grade local encryption on your device before a file ever touches the cloud or a network, generating secure, time-sensitive download links.
We specialize in high-velocity engineering, helping you move from concept to MVP in record time.
Our design team blends luxury aesthetics with functional simplicity to create sleek, minimal interfaces that captivate users
The world of tech is shifting toward decentralization and data-driven insights, and we are already there

Military-grade encryption, secure auth flows, and transparent privacy practices that build lasting user trust.
Security compliance built to Apple and Google's standards — reviewed before you submit, not after rejection.
Incident response playbooks and real-time monitoring so your team can contain and resolve threats fast.
Architected to handle growing user bases, new features, and regulatory changes without emergency rework.
App Stop takes ownership of both product thinking and execution. We combine design clarity, engineering discipline, and market context to ship experiences that are fast, usable, and ready to scale.
OUR PROJECT PROCESS
Understand user behavior, pain points, and product goals before writing a single line of code.
Translate validated insights into thoughtful UI/UX and robust engineering implementation.
Ship confidently with performance checks, deployment planning, and post-launch support.
FAQ
During development — always. Retrofitting security into a live product is exponentially more expensive, more disruptive, and riskier than building it in from the start. We make security a delivery requirement, not an afterthought.
Yes. A pre-launch security review is one of the most cost-effective things you can do. We identify and remediate vulnerabilities before they reach production — or before Apple and Google's automated scanners flag them for you.
No. Early-stage products are often the most vulnerable — and the hardest hit when something goes wrong. We work with startups, scale-ups, and enterprises to build the right level of security for their current stage and risk profile.